How ADFS & Azure AD Connect Can Impact Microsoft 365 Users
Microsoft Office 365 Performance
Office 365, now called Microsoft 365, is no doubt, the biggest cloud service on the planet. Despite its size and market share, it’s important to remember that cloud services are reliant on-premises components. If you want to ensure the availability and performance of Exchange online, Teams or SharePoint, you need to make sure that your Microsoft identities are working fine too. That is why we’ve just released new functionalities for our Microsoft Office 365 service quality monitoring product. Martello’s Vantage DX is now able to test, alert and report on the availability and performance of your Microsoft ADFS and Azure AD Connect in parallel with our unique capabilities to monitor the end-user experience of the Microsoft Office 365 suite.
Want to see how it works? Sign up for our 14-day free trial and test our solution directly in your environment. Get started today!
Let’s start with ADFS
As you know, Active Directory Federation Services (ADFS) provides users with single sign-on access to systems and applications across organizational boundaries. It is usually used as an identity management option for Office 365.
Ensuring the availability of this service is critical. If your ADFS infrastructure is unavailable, end-users won’t be able to log into Office 365 services.
One of the most common issues with ADFS is disconnection. If you’ve ever tried signing into Office 365 or other Microsoft cloud services and failed to connect, you know how frustrating this can be. If users sign into a cloud service with a federated user account, the connection to ADFS will fail if they try to connect remotely or use an email connection to sign in.
So, what causes the missed connection? The ADFS service might not be exposed correctly to the Internet, impacting your ADFS server proxy. This causes expired SSL certificates, incorrect IIS authentication endpoint configurations, and/or distrust between the ADFS proxy server and the ADFS Federation Service.
There are three ways to fix these Microsoft Office 365 issues:
- Try troubleshooting the ADFS SSL certificate issues on the ADFS service by updating the SSL certificate on the proxy service.
- Retune the ADFS proxy server IIS authentication settings to default.
- Rerun the ADFS Proxy Configuration wizard from the Administrative Tools interface.
To fix ADFS issue you need to be aware of them. It is not because a user can’t log into Microsoft service that it is automatically ADFS.
We’ve seen from customers that many were trying to troubleshoot a login error for hours before realizing the root cause of the issue was ADFS.
For this reason, it is important to test in real time the ADFS service and make sure it performs well to avoid any issue.
That is what Martello Gizmo is doing for you.
Martello Gizmo tests the ADFS exactly as a user would, by trying to perform a full authentication to Microsoft Office 365. Martello Gizmo sends the request against Windows credentials and makes sure the ADFS server is responding to the request with the token quickly.
Our Office 365 monitoring solution checks the time taken by the overall process, displays the metrics in real time and alerts in case of abnormal latency.
The result allows administrators to quickly identify and troubleshoot ADFS issues from a single dashboard, reducing headaches and improving overall performance in your Office 365 environment.

Another ADFS point of failure that we often see from our customers is the certificates.
ADFS requires several certificates to secure the communication, enable user authentication and authorization requests to federation servers- federation servers proxies an ADFS enabled Web servers.
It is critical to make sure these certificates are always up to date.
Martello Gizmo constantly checks the status of these certificates and warns you as soon as one of them is set to expire in the next 30 days. With that feature you will never miss a renewal and you’ll be sure that user authentication problems are not caused by this avoidable issue.
See how you can empower enterprise IT to ensure a product Microsoft 365 experience. Give it a test run today!
Let’s Talk Now About Azure AD Connect
The other pillar of Microsoft identities also plays a critical part in the ability for users to connect to their Microsoft Office 365 service. Again, this service is installed on-premises on a Windows server.
As you know, Azure AD Connect is responsible for the synchronization between your Active Directory identities and Microsoft Office 365.
If the synchronization is not working, the established connection will still work, but any change in the on-premises directory will not show on Microsoft 365. So, you will have connection issues with your users.
Once again, if you do not monitor the status of this synchronization, it will be difficult for you to find the root cause of connections to cloud services issues.
We’ve seen at large enterprises that it is not the first thing they check, which makes sense because plenty of reasons that can lead to user’s authentication issue.
That is why it is important to keep an eye on it. This is exactly what Martello Gizmo is doing.
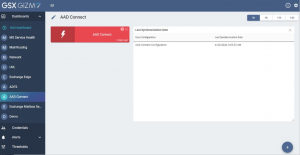
Martello’s Vantage DX constantly check the status and the time of the last synchronization between your AD and Microsoft 365. If the last synchronization failed or just never happen, you will be alerted.
Therefore, you won’t spent time troubleshooting a user’s connection issue caused by Azure AD Connect since you’ll have the alert and the information, right under your eyes at the minute it happens.
As you see, Microsoft Office 365 is a cloud service that requires hybrid component to be available for your users. At Martello, we understand that.
That is also why our latest version provides so many features for Hybrid Exchange deployments. The future is the cloud, but the future is connected to the present where on-premises servers and services are still indispensable to allow users to be more productive.
Learn more about Martello’s service management solution for your Azure services here.